Synology Server Set Up & Initialization
We Build-to-Order your PC according to your needs

We provide assistance and troubleshooting for technology-related issues, ensuring smooth operation and optimal performance of computer systems and software.
We offer expert advice and solutions to businesses on technology-related matters, helping them optimize their IT infrastructure, processes, and strategies for growth.
Build-to-order PCs are customized computers assembled to meet specific customer requirements, offering flexibility in hardware selection, performance, and budget.

We Build-to-Order your PC according to your needs
Setting up and initializing a Synology server involves a few key steps to ensure smooth operation and optimal performance:
Hardware Setup: Unpack the Synology server and connect it to power and network. Install any additional hard drives or SSDs if necessary.
Initial Configuration: Access the Synology DiskStation Manager (DSM) interface through a web browser using the server’s IP address. Follow the setup wizard to configure basic settings such as language, timezone, and administrative account details.
Volume and Storage Pool Creation: Create storage volumes and storage pools based on your storage needs and redundancy requirements. Synology offers various RAID configurations for data protection and performance optimization.
Network Configuration: Set up network settings, including LAN, WAN, and port forwarding if necessary. Ensure proper network connectivity for remote access and data transfers.
Services and Applications: Install and configure desired services and applications from the Synology Package Center. This may include file sharing, backup solutions, multimedia streaming, surveillance, and more.
Security Settings: Implement security measures such as firewall settings, user permissions, and encryption to safeguard data and prevent unauthorized access.
Backup and Disaster Recovery: Set up backup tasks to ensure data redundancy and disaster recovery. Synology offers built-in backup solutions as well as compatibility with third-party backup software.
Monitoring and Maintenance: Configure system monitoring tools to keep track of server performance, storage usage, and system health. Perform regular maintenance tasks such as firmware updates and disk health checks.
By following these steps, you can effectively set up and initialize your Synology server to meet your specific storage, networking, and security requirements while maximizing its capabilities for your business or personal use.

We Build-to-Order your PC according to your needs

We Build-to-Order your PC according to your needs
Studying Business Information Systems with a BSC at the University of Wales offers a comprehensive understanding of IT and business management, equipping students for dynamic careers in technology-driven industries.
Attending high school at the American College of Greece offers a diverse and rigorous academic curriculum within a supportive community, preparing students for success in higher education and beyond.
Unlimited remote support during business hours (9 am to 5 pm, Monday to Friday)
Unlimited remote support during business hours
On-site support for up to 5 hours per month
Basic network monitoring and maintenance
Troubleshooting and resolution of hardware and software issues
Email and phone support for critical issues outside of business hours (response within 24 hours)
Unlimited remote support 24/7
Unlimited remote support 24/7
On-site support for up to 10 hours per month
Proactive network monitoring and maintenance, including security patches and updates
Comprehensive hardware and software troubleshooting and resolution
Priority email, phone, and chat support for all issues
Email and phone support for critical issues outside of business hours (response within 24 hours)
Regular security audits and vulnerability assessments
Unlimited remote and on-site support 24/7
Unlimited remote and on-site support 24/7
Priority response time of 2 hours for critical issues
Advanced network monitoring and maintenance with intrusion detection and prevention systems
Advanced troubleshooting and resolution for complex hardware and software issues
Customized security solutions tailored to your business needs
Regular on-site visits for system optimization and user training
Quarterly strategy meetings to align IT with business goals and objectives

The National Security Agency (NSA) is the font of information security wisdom for the US defense and intelligence communities. But apparently, the NSA’s own network security is so weak that a single administrator was able to hijack the credentials of a number of NSA employees with high-level security clearances and use them to download data from the agency’s internal networks. That administrator was Edward Snowden.
Under Department of Defense (DOD) Directive 8500.2, the director of the NSA, Gen. Keith Alexander, is tasked with approving all the cryptographic hardware and software used by the DOD. The NSA also provides “information assurance” and information system security engineering services to DOD branches and agencies. And along with the National Institute of Standards and Technology, the NSA maintains the master guide for DOD information security systems: the Information Assurance Technical Framework (IATF).
But in what appears to be a case of “do as I say, not as I do,” the NSA’s internal IT security schemes allowed Snowden, a contractor sysadmin, to pull off a classic insider attack on the agency. An investigation by NBC found that Snowden had used the digital identities of several upper-level NSA officials to log into NSAnet, the agency’s intranet—giving him access to data far beyond the needs of a lowly system administrator.
The systems accessed by Snowden limit access by user role, so he could not have used his own credentials on them without overriding access controls. Officials familiar with the case told NBC that Snowden had obtained the “profiles” of a number of NSA employees that have been identified through forensic examination of logs, finding periods when the employees were traveling but their accounts were still used to access the intranet. If Snowden used administrative privileges to reset their passwords, failed logins might have flagged a problem—but they might have simply been shrugged off as passwords forgotten over vacation.
In order to pull this off without raising alarms, Snowden would have needed access to the full credentials of the users whose identities he borrowed. He would have needed to somehow either gain access to the public key infrastructure (PKI) keys found in their user authentication or he would have needed to override multi-factor authentication to gain access to the systems. He also would have needed to avoid detection by audit logs in making those changes (or delete the record of changes after the fact). He managed to do all of these things, download the content, and get it past the NSA’s physical security.
Some or all of this trouble could have been avoided if the NSA had followed its own playbook a bit more closely and used administrative and security best practices that are common across government, the financial industry, and other networks where access control auditing and the non-repudiation of data are mandated by laws, regulations, and the nature of the business. Giving an administrator the ability to gain access to user credentials—and the log systems that monitor changes to those credentials—is a classic bad move in network security. As Oracle points out in its documentation for its Enterprise Manager administration tool, “Giving the same level of access to all systems to all administrators is dangerous.” In most sensitive enterprise systems, administrators’ access powers are limited to very specific roles to prevent giving them the power to compromise multiple systems, making it more difficult for an insider to attack systems and cover his or her tracks.
In the wake of the Snowden breach, Gen. Alexander announced that the NSA would implement two-person administrative requirements; that’s a measure that’s been recommended by the IATF for over a decade. “Limits can be placed on each individual’s authorized privileges,” the IATF says. “The application and the security features it provides can also partly counter these threats with features such as audit, two-person administrative requirements, and covert access prevention and detection.” Covert access prevention and detection would include monitoring login locations and watching for attempts to get at data from ways other than through the approved front-end (such as trying to pull directly from a disk directory instead of going through the intranet server).
Networks classified as secret and above at the DOD are supposed to be protected by layers of intrusion detection and automated auditing systems. Security event information management (SEIM) systems and other internal network monitoring tools can be configured to catch log events that human eyes might miss—like a user from Fort Meade logging in unexpectedly from a station in Hawaii. A number of SEIM systems are used by organizations within the DOD for security auditing.
But based on statements by Gen. Alexander and reports about the breach, it appears that the NSA—the agency responsible for monitoring the networks of the world—didn’t have a great deal of automated monitoring inside its own firewalls. Instead of using automated systems, the NSA apparently depends on an army of system administrators for its internal defenses—administrators like Edward Snowden. With masses of log data to check through, Snowden likely slipped past the eyes of other administrators or managed to delete or alter log records before they raised suspicion.
The NSA reportedly still doesn’t know the extent of what Snowden extracted from the agency’s intranet, and investigators are poring over access logs to try to find conflicts that would indicate which users’ accounts Snowden used. Given the apparent superuser powers Snowden was able to wield—and the apparent lack of insider threat protection the agency had in place—they may never fully know.
This post was originally published on arstechnica.com

Hackers suspected of working for the Chinese government are mass exploiting a pair of critical vulnerabilities that give them complete control of virtual private network appliances sold by Ivanti, researchers said.
As of Tuesday morning, security company Censys detected 492 Ivanti VPNs that remained infected out of 26,000 devices exposed to the Internet. More than a quarter of the compromised VPNs—121—resided in the US. The three countries with the next biggest concentrations were Germany with 26, South Korea with 24, and China with 21.
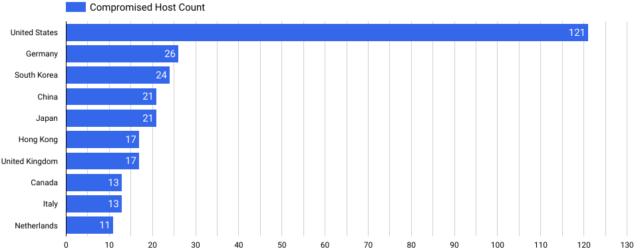
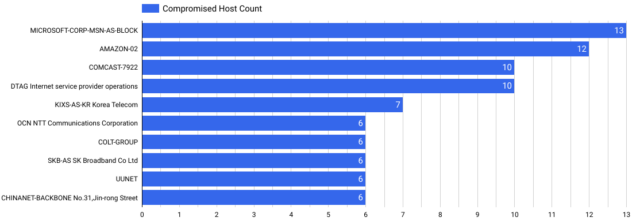
Microsoft’s customer cloud service hosted the most infected devices with 13, followed by cloud environments from Amazon with 12, and Comcast at 10.
“We conducted a secondary scan on all Ivanti Connect Secure servers in our dataset and found 412 unique hosts with this backdoor,” Censys researchers wrote. “Additionally, we found 22 distinct ‘variants’ (or unique callback methods), which could indicate multiple attackers or a single attacker evolving their tactics.”
In an email, members of the Censys research team said evidence suggests that the people infecting the devices are motivated by espionage objectives. That theory aligns with reports published recently by security firms Volexity and Mandiant. Volexity researchers said they suspect the threat actor, tracked as UTA0178, is a “Chinese nation-state-level threat actor.” Mandiant, which tracks the attack group as UNC5221, said the hackers are pursuing an “espionage-motivated APT campaign.”
All civilian governmental agencies have been mandated to take corrective action to prevent exploitation. Federal Civilian Executive Branch agencies had until 11:59 pm Monday to follow the mandate, which was issued Friday by the Cybersecurity and Infrastructure Security Agency. Ivanti has yet to release patches to fix the vulnerabilities. In their absence, Ivanti, CISA, and security companies are urging affected users to follow mitigation and recovery guidance provided by Ivanti that include preventative measures to block exploitation and steps for customers to rebuild and upgrade their systems if they detect exploitation.
“This directive is no surprise, considering the worldwide mass exploitation observed since Ivanti initially revealed the vulnerabilities on January 10,” Censys researchers wrote. “These vulnerabilities are particularly serious given the severity, widespread exposure of these systems, and the complexity of mitigation—especially given the absence of an official patch from the vendor as of the current writing.”
When Avanti disclosed the vulnerabilities on January 10, the company said it would release patches on a staggered basis starting this week. The company has not issued a public statement since confirming the patch was still on schedule.
VPNs are an ideal device for hackers to infect because the always-on appliances sit at the very edge of the network, where they accept incoming connections. Because the VPNs must communicate with broad parts of the internal network, hackers who compromise the devices can then expand their presence to other areas. When exploited in unison, the vulnerabilities, tracked as CVE-2023-46805 and CVE-2024-21887, allow attackers to remotely execute code on servers. All supported versions of the Ivanti Connect Secure—often abbreviated as ICS and formerly known as Pulse Secure—are affected.
The ongoing attacks use the exploits to install a host of malware that acts as a backdoor. The hackers then use the malware to harvest as many credentials as possible belonging to various employees and devices on the infected network and to rifle around the network. Despite the use of this malware, the attackers largely employ an approach known as “living off the land,” which uses legitimate software and tools so they’re harder to detect.
The posts linked above from Volexity and Mandiant provide extensive descriptions of how the malware behaves and methods for detecting infections.
Given the severity of the vulnerabilities and the consequences that follow when they’re exploited, all users of affected products should prioritize mitigation of these vulnerabilities, even if that means temporarily suspending VPN usage.
This post was originally published on arstechnica.com

An online activist site has collected 300,000 signatures in opposition to a pending “cyber-security” bill that critics say would allow increased government spying on the Internet. The petition focuses on a bill by Rep. Mike Rogers (R-MI), but his legislation is one of at least four proposals now being considered by Congress.
According to Jerry Brito, a researcher at the Mercatus Center at George Mason University, there are four competing bills because the two parties—and the two houses of Congress—disagree about how best to deal with online security issues. One point of controversy is over who will take the lead on the issue, the Department of Homeland Security or the National Security Agency. A bill by Senator Joseph Lieberman (I-CT), which would have given the leading role to DHS, was originally expected to pass easily through the Senate. But several Senate Republicans, led by Sen. John McCain (R-AZ) were dissatisfied with the Lieberman bill and introduced competing legislation that envisioned a larger role for the NSA.
The ensuing partisan gridlock in the Senate created an opening for the House to act, and at least two pieces of legislation have been introduced in the lower chamber. The leading bill, by Rep. Mike Rogers (R-MI), follows Senate Republicans in allowing sharing with the NSA. It focuses on facilitating information sharing, both between the government and the private sector, and between private network operators. It exempts “cyber-security” information-sharing from other legal restrictions, and it immunizes network providers from liability for failing to act on information they receive under the provisions of the act.
A competing bill sponsored by Rep. Dan Lungren (R-CA), places stricter limits on which agencies can receive information and what they can do with it.
Ars Technica asked Jim Dempsey of the Center for Democracy and Technology to evaluate the competing bills. He argued that all four bills go too far in allowing private companies broad authority to share information with the government. He said the Rogers and McCain bills, in particular, “allow private companies very broadly to share cyber-security information with the government,” including the NSA.
Dempsey argued that was troubling. “The NSA is responsible for protecting the government’s classified systems,” he said. “It’s not responsible for protecting private networks. The agency should not be getting routine disclosure of information about private information over private networks.” Dempsey said the House bill by Rep. Dan Lungren (R-CA) is the narrowest of the four bills, requiring that information shared with the government only be used for “cyber-security” purposes.
Still, Dempsey questioned whether new legislation authorizing private-to-government information sharing was needed at all. “If you’re being attacked, either in the real world or the cyber world, you’re always permitted to disclose that information to the government,” he said. He said that CDT could support legislation to clarify that private firms are allowed to report network intrusions to the government, but he said the current proposals are a “classic case of overreach.”
Dempsey did voice support for a few other tweaks to the law. He suggested Congress should update wiretapping law to make it clear that service providers are allowed to share information about attacks with one another. Under existing law, he said, service providers are allowed to monitor their own networks for security purposes, but it’s unclear how much information a network provider can share with other networks to help coordinate defenses against online attacks.
Dempsey said this approach—focusing on narrow fixes to existing statutes—hasn’t been popular on Capitol Hill. He said the lawmakers he has spoken to have expressed doubt about whether wiretapping law was the only obstacle to effective network security measures. But rather than trying to figure out what other legal obstacles to information sharing might exist, and fixing them directly, the leading bills all grant broad exemptions for sharing information related to “cyber-security.”
That has the obvious advantage of reassuring network providers that they can share information without legal problems. But it could also have significant unintended consequences. By granting firms who share information broad immunity from other provisions of law, Congress may be effectively changing any number of other statutes. Dempsey described it as a “blunt instrument,” and warned it could become a loophole for circumventing any number of important privacy protections.
Brito is even more skeptical than Dempsey about the need for new legislation. He argues that private parties already have ample incentives and capabilities to lock down their own networks. If the government has information that would be helpful to the private sector, it should share it, he said. That doesn’t require action by Congress.
The breadth of the proposals, and especially Rep. Rogers’s Cyber Intelligence Sharing and Protection Act, has sparked a growing public backlash, with some opponents comparing the bill to the Stop Online Piracy Act that was defeated in January. The comparison is a bit of a stretch; SOPA was focused on blocking access to information, while the current crop of “cyber-security” bills are more focused on network monitoring and information sharing with the government.
But the bills do have one important similarity: they’re likely to attract many of the same enemies. The Internet freedom activists who helped kill SOPA in January have been looking for their next target. And CISPA seems like a good choice.
This post was originally published on arstechnica.com
I am available for freelance work. Get in touch and we will discuss the best solution for your needs.
Phone: +306937372643 Email: info@techminers.gr
